- HOME
- Email Marketing
- Defeat email spoofing: An email security guide to protect your brand
Defeat email spoofing: An email security guide to protect your brand
- Last Updated : April 3, 2025
- 630 Views
- 6 Min Read
What is email spoofing?
Have you ever received an email that looked legitimate but felt off?
Or worse, have any of your customers received an email that looks like it was from your company, but it was not?
That is email spoofing.
Email spoofing is the act where a person with malicious intent impersonates the email address of a legitimate business to deceive the recipient. If you're representing a business, someone might be emailing people pretending to be from your company to commit email fraud. Scary, isn't it?
This blog post will take you through what email spoofing is, how it happens, and what measures you can take to prevent email spoofing.
How does email spoofing happen?
Consider a malicious actor. Their job is to send spoofed emails pretending to be from actual companies. When innocent people believe them, the victims tend to click on the links in emails or provide personal information and fall into trouble.
The malicious actor turns to an ecommerce store. They plan to send spoofed emails to those customers.They check the DMARC record of the store's domain. They find out that the ecommerce store has not set up SPF and DKIM validations and does not have a DMARC reject policy.
Now very happy, the malicious actor spoofs their email address to look like the store's official email address.
Now, they email the store's customers, announcing that the recipient won a raffle. The email asks the recipients to open a link to claim their prize. Since the sender address looks like it came from the store, some unassuming recipients click on the link and their device gets hacked.
Why is email spoofing dangerous?
Email spoofing can lead to huge problems not only for the email recipients, but also for the companies or individuals who are being impersonated. Spoofing can cause:
Financial losses
Malicious actors use email spoofing to pretend to represent a company and trick victims into sending money to win a prize. They may also pretend to be a company executive to trick employees into wiring money or purchasing gift cards. Email spoofing, where scammers pretend to be company executives is known as business email compromise (BEC) and in the last decade alone, BEC has cost $55.5B worldwide.
Data breaches
Even if they fail at stealing money, email spoofers often steal credentials or lure victims into providing sensitive information, leading to personal or company-wide data theft. They may then sell this data or use it to steal money.
Damaged reputations
Regardless of the kind of loss your customers, employees, or organization face, an act of email spoofing always brings down your sender reputation. It can make your organization appear insecure or prone to breaches. Recipients may also think a potential scammer works within your organization, thereby affecting your organization's reputation.
Legal consequences
Depending on your organization or customers' geographical locations, you may be subject to data protection regulations. If the regulatory authorities deem you didn't take enough data security measures, you may also be imposed heavy fines.
Email deliverability
When someone with malicious intent spoofs your domain and sends spam emails, it affects your domain reputation. This in turn causes email providers to wrongly mark your legitimate emails as spam, bringing down your email deliverability. So your emails may not land in the recipients' inbox, or your email address may even get blocked.
Note: Want to learn what other factors affect email deliverability? Check out this deliverability guide.
What does a spoofed email look like?
Here are the components to look for in a spoofed email:
Display name spoofing is when the display name in the spoofed email is the same as or similar to an actual name used by someone from the company.
Domain spoofing is when the spoofer forges the domain name of the company itself. In this case, along with the display name, the email domain also appears to be the same.
Suspicious sender address is an easy giveaway of a spoofed email. When the spoofer may be able to mimic the display name, it is often more difficult to spoof the domain name. So while the display name might be that of a real person, the domain name attached to it would be different.
Beware of urgency or threatening language. Malicious actors often resort to threats or a sense of urgency. This gives their victims less time to think and makes them act on fear or impulse.
The email promises prizes or giveaway wins. The offer of a reward or prize is alluring and makes unsuspecting people provide personal information to claim the prizes. The email may also ask the recipient to click on unusual looking attachments or links, which will download malware to hack the victim's devices.
The email may be visually inconsistent, such as a wrong or older logo and a different formatting from the ones usually sent by the company. Although email spoofers have now gotten better at replicating the visual style, some spoofed emails still obviously give themselves away as fake.
How to stop email spoofing
Email spoofing can be prevented by implementing multiple email authentication methods, such as SPF, DKIM, and DMARC. While each method serves a purpose of its own, the combined power of these is a powerful way to protect your email domain from being spoofed.
Did you know if you are a high-volume email sender to users with Gmail and Yahoo mail addresses, SPF and DKIM are mandatory?
Sender Policy Framework (SPF)
SPF is an email authentication protocol that is used to verify sender identity.
To implement SPF, you authenticate the IP addresses or mail servers that are allowed to send emails on your behalf. When an email is received at the receiving server, it goes to the Domain Name Server (DNS) and looks up the authorized IP addresses for your domain.
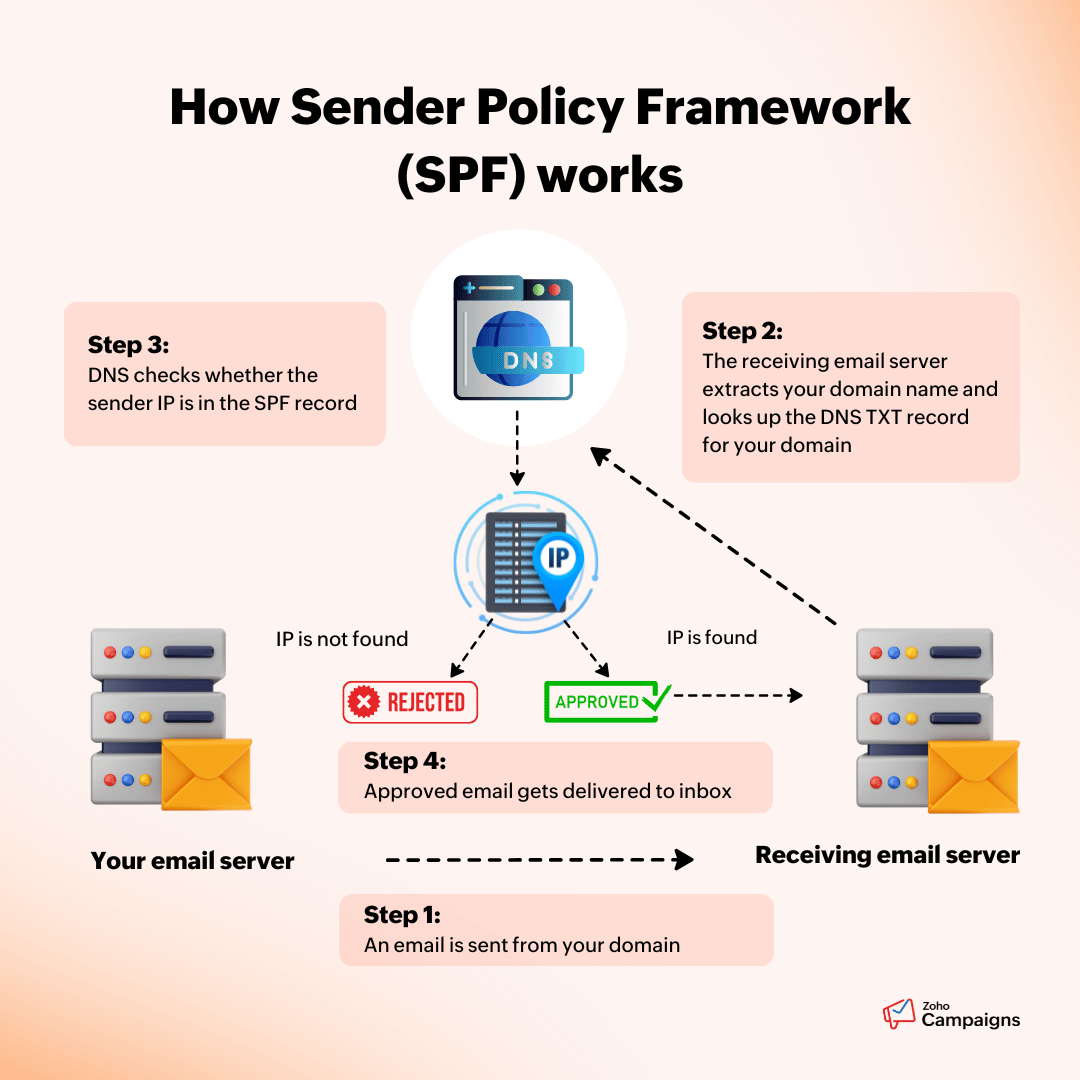
The email is only delivered to the recipients' inbox if it's sent from an approved IP address and passes the SPF validation.
By setting up SPF records, you can improve deliverability, reduce spam, and prevent email spoofing.
DomainKeys Identified Mail (DKIM)
DKIM is a digital signature that gets added to every email you send. It is a complementary partner to go with your SPF records. In addition to verifying the sender's authenticity, it also helps ensure that the email content wasn't tampered with or modified in transit.
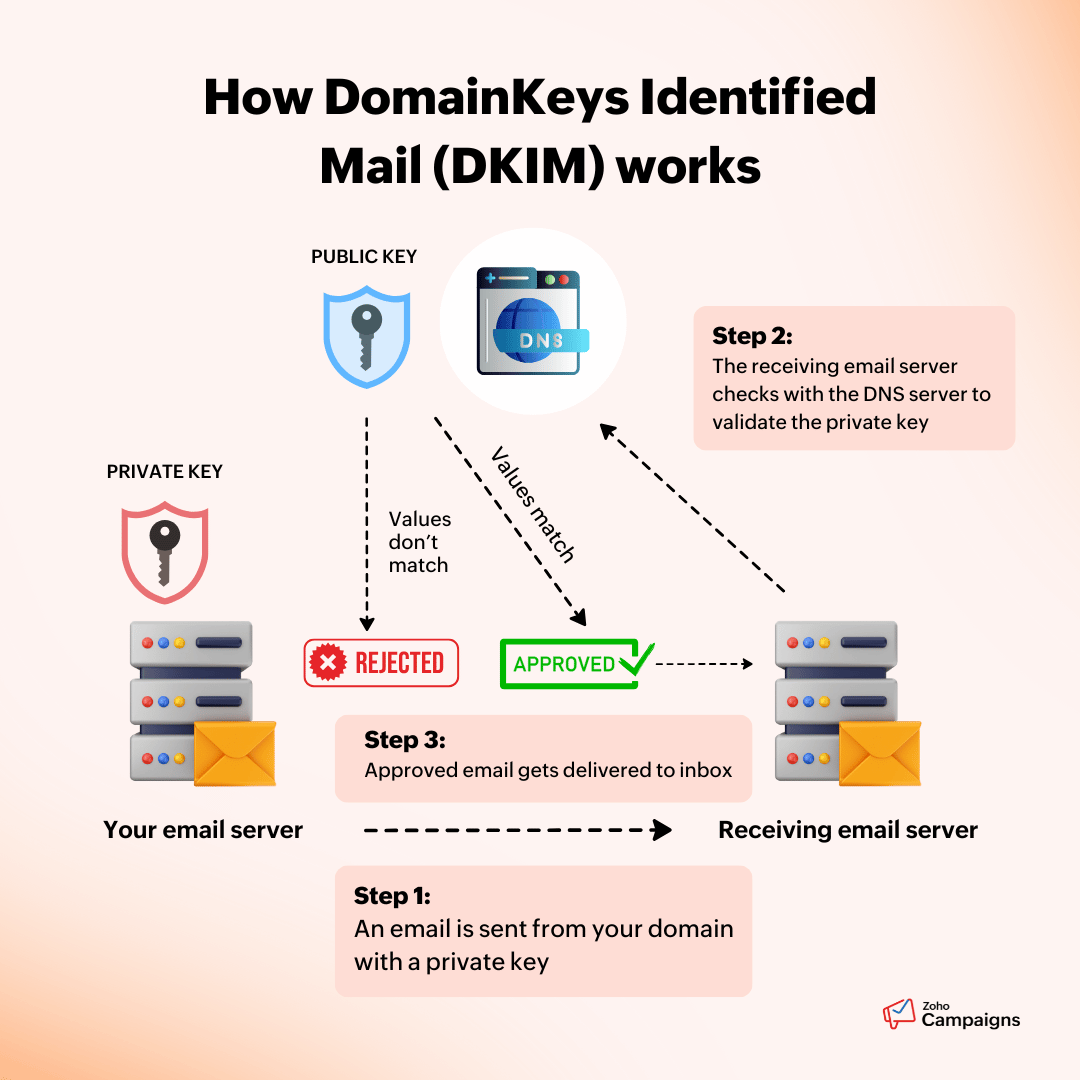
To implement DKIM, you upload a public key to the DNS server. When an email is sent from your server, the email content and headers are encrypted to create a hash of those values. The email server then signs that hash with a private key that only your email server has.
When the email is received at the recipient's email server, it pulls the public key from the DNS server and validates the hash in the private key. If the values match, then the recipient server knows that the email was not tampered with and delivers the email to the recipient.
In addition to preventing tampered messages from getting delivered, this is another way to ensure no one spoofs emails pretending to be you as they cannot have your private key.
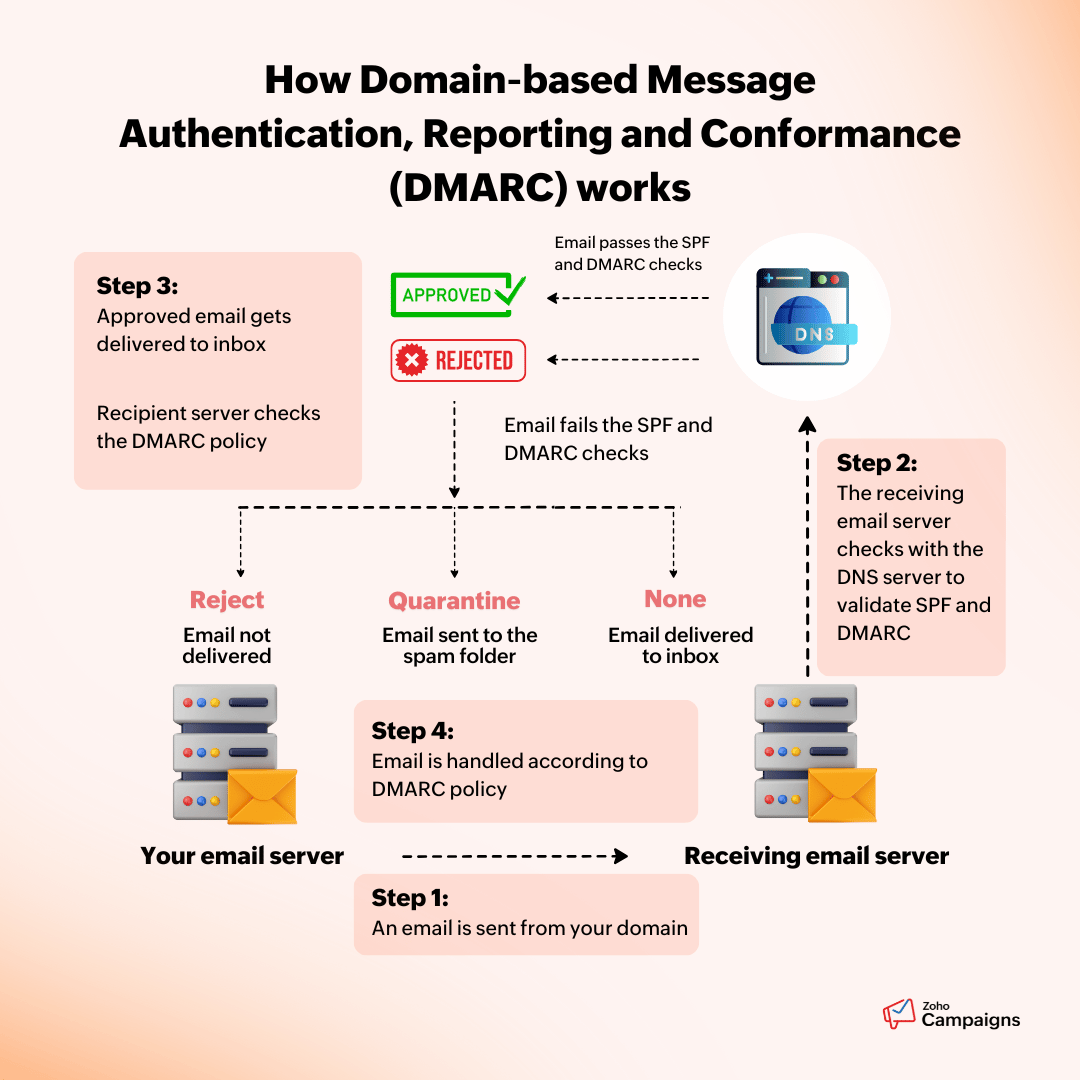
Domain-based Message Authentication, Reporting and Conformance (DMARC)
DMARC is an advanced authentication method used to prevent email spoofing; it builds off of SPF and DKIM. It gives directions on what happens when SPF or DKIM checks on an email fail.
DMARC allows you to publish a policy that provides instructions to the recipient mailbox servers about what happens when an email is unauthenticated. You can instruct for one of the following three actions to occur when an email fails SPF or DKIM.
Action 1: None
This means no action will be taken even if the email doesn't pass SPF or DKIM checks. The email will be sent to the recipient's inbox without any further action.
Action 2: Quarantine
The quarantine action still allows the email to be sent even if it doesn't pass SPF or DKIM, but the email will most likely land in the recipient's spam folder.
Action 3: Reject
When you choose this option, any email that fails SPF or DKIM will get rejected and never reaches the recipients' mail boxes.
How Zoho Campaigns helps you prevent email spoofing and protect your domain
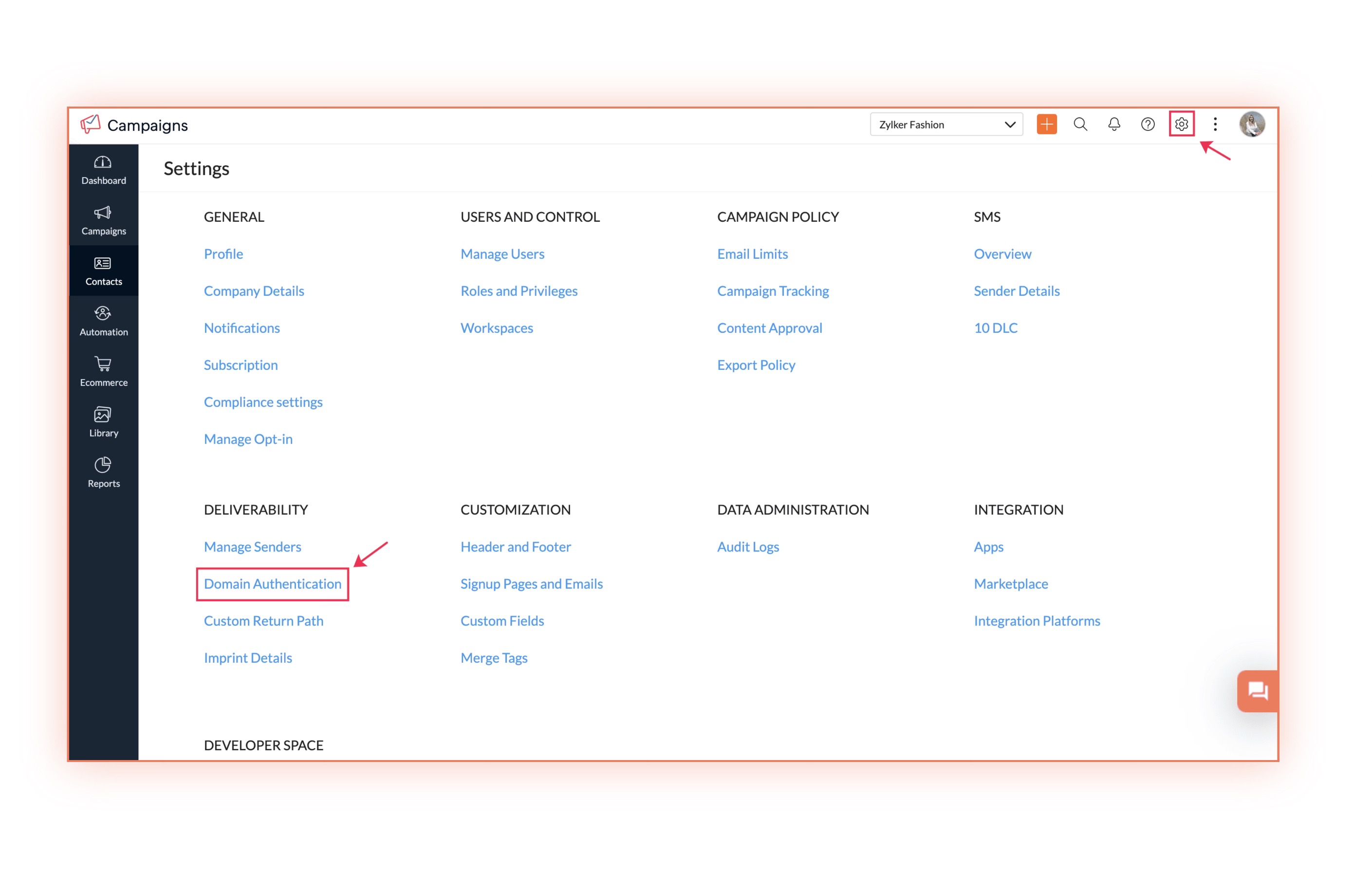
Zoho Campaigns enables every user to quickly set up SPF and DKIM records to authenticate their domain.
If an email passes SPF and DKIM validations, DMARC policy will not be applied. But if SPF or DKIM fail, then the recipient server will check the DMARC policy. Note that DMARC policies can be enabled only after SPF and DKIM, as otherwise, DMARC will fail.
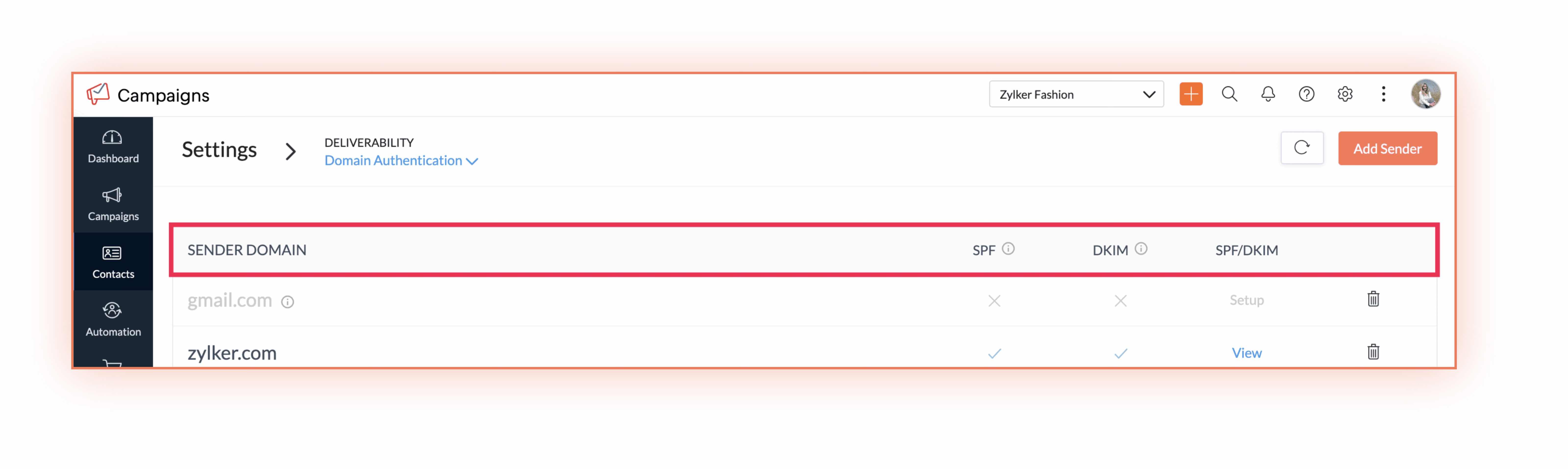
Once you finish SPF and DKIM authentication for your domain, you can configure the DMARC policy in your domain's DNS records. You can learn more about setting up DMARC records here.
Setting up SPF and DKIM not only helps combat email spoofing, but also helps increase your email deliverability. In addition to SPF and DKIM, Zoho Campaigns also provides a number of other deliverability-focused features to ensure your emails always reach inboxes.
Conclusion
With scammers sending more than 3.1 billion spoofed emails every day, it's crucial to be vigilant as an organization. Email spoofing is evolving, and staying complacent comes with the risk of financial or reputational damage.
By proactively implementing email authentication protocols like SPF, DKIM and DMARC, companies can significantly reduce the risk of falling prey to email spoofing.
Try Zoho Campaigns today to enhance your email security.
 Vidhya Vijayaraghavan
Vidhya VijayaraghavanHi! I'm Vidhya, a storyteller and problem solver. I wholeheartedly believe that B2B content doesn't have to be boring.
When not writing or having a writer's block, you can catch me reading, puzzling, or volunteering.
I'm game for a conversation about anything, especially B2B SaaS marketing (and cats too!).